Something’s wrong with the security market.
Let's align our incentives to customers' desired outcomes: fewer, less costly breaches.
Help! I’ve fallen into breach stats, and I can’t get up.
I rant to friends, colleagues, and my infinitely patient spouse about the failing cybersecurity market.
Yes, failing.
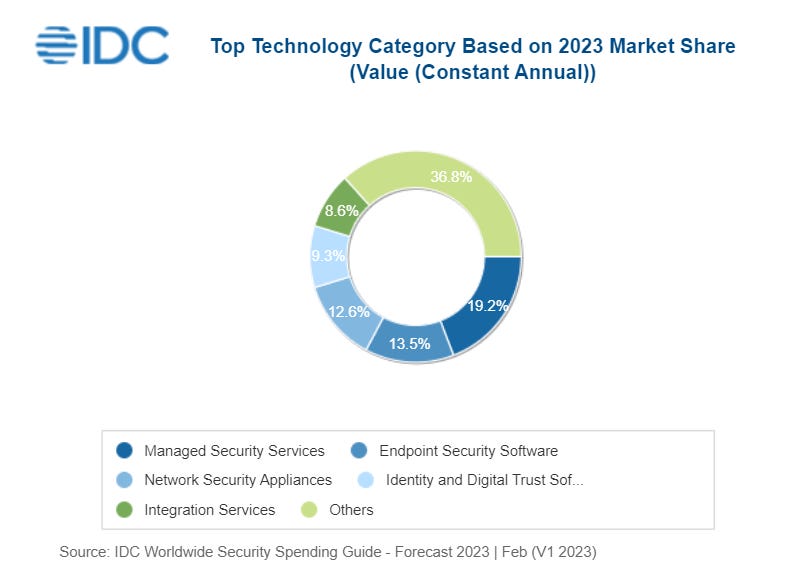
Over the last four years, venture firms invested just over $55B in cybersecurity. Yet, the global average cost of a security breach increased by 30%. 83% of companies experienced a data breach and the vast majority pass on these costs to their customers. They must because they plan to spend almost $220B in 2023 to solve their cybersecurity problems.
Meanwhile, private company valuations shot through the roof, raking in cash at unprecedented rates–Wiz boasts about getting to $100M in eighteen months, making them the fastest-growing security vendor ever. Most make lofty claims about keeping bad guys out through automated detection and response, using machine learning and artificial intelligence to predict when and where attacks will occur, and giving security practitioners unmatched visibility into and control over their security posture. The claims sound great on paper but underdeliver the outcomes customers want: fewer breaches and lower costs per breach.
Whose fault is this?
The industry pushes the blame on the customer. Managed security service providers message this blame shift aggressively, presumably because of how close they are to the point of failure. Customers, they tell us, equate spending with security, invest ineffectively, don’t leverage outside security expertise, or just need to spend more.
Spend more on what?
Companies are already spending a lot on defense.
Customers are pouring money into defending themselves. Cybersecurity spending increased by almost 80% over the last four years.
Companies spend tens of billions on network security products–critical as they go multi-cloud and hybrid–only to catch the blame for not patching quickly enough when vendors (looking at you Fortinet and SonicWall) deliver products with dozens of critical CVEs. The severity of the flaws leaves customers without workarounds or requires wholesale upgrades of hundreds or thousands of endpoints. Already overburdened teams make massive production changes under tremendous stress.
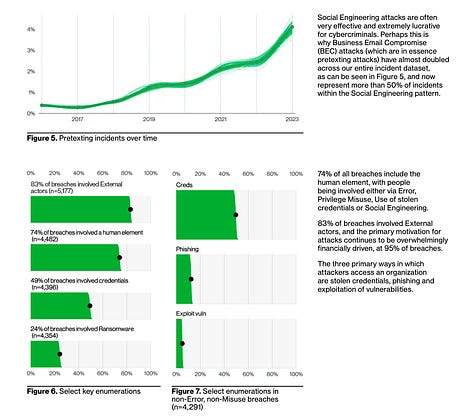
Companies spend tens of billions on identity products, yet three-quarters of all breaches include the human element, and half involve stolen credentials. Users are grossly over-provisioned, over-permissioned, and under-credentialed.
I recall talking to one customer with two hundred thousand users and six million roles and entitlements, generating seventy million compliance findings per quarter. Whole new market categories have popped up to solve this problem. And now, customers must spend even more on the new vendor’s solution to get what they paid the first vendor to solve.
The cost, frequency, and severity of breaches grow alarmingly.
Last year 422M users were impacted by data breaches, and more than 22B records were compromised. The frequency and severity of breaches continue to increase, up almost 40% in 2022. An average customer needs 277 days to identify and contain a breach.
According to IBM and Ponemon Institute research, the average global cost of a breach rose from $3.8M in 2020 to over $5M in 2023. US numbers are dire, with average costs topping $9M. And, certain industries take proper beatings–healthcare comes in at $10.10M, a 42% increase since 2020.
On May 1, 2021, I was in a Scripps emergency room seeking care for my father, who was seriously injured in a fall. A victim of a ransomware attack, all of Scripps’ computer systems were down, and they were processing patients on paper. We waited in a hallway for twelve hours while he bled through the bandages applied by paramedics hours before, unable to get a room, a doctor's attention, pain medication, or much-needed X-rays. The medical staff were frantic, and only the grizzled veterans had any experience with paper records.
Scripps lost 1.2 million patient records in that attack, and their systems were offline for over three weeks. They lost an estimated $113M in revenue and paid affected patients a $3.5M settlement.
The blame game.
Despite the healthcare industry spending over $12B on cybersecurity in 2020, the cybersecurity industry persists in slinging blame on customers, exemplified best by this quote from the ironically named Alexa Slinger, an identity expert from the company OneLogin:
“The health care industry is notorious for underspending on IT, and malicious actors know the data they can glean from a health care hack is especially lucrative on the dark market…”
OneLogin claims revenue of roughly $60M from six thousand customers. They built that business on the back of $175M in funding. So this is pretty sharp criticism from a security company that was breached twice, once in 2016 and again in 2017, with the second breach affecting ALL of their customers:
“All customers served by our US data center are affected; customer data was compromised, including the ability to decrypt encrypted data.”
Ouch.
Security companies are vulnerable, too. Okta (twice), Auth0, and, most recently, Jumpcloud–who had to revoke all their API keys–are just a small handful of security vendors who have suffered breaches while positioning themselves as a solution to the problem.
Dozens of other vendors foist dazzling marketing on customers with bold claims about how well they protect them from ransomware and other attacks. One Identity, who acquired OneLogin, has some nifty marketing for their “complete cybersecurity for healthcare.”

It’s hard to make this stuff up.
I wonder how much of One Identity/OneLogin’s estimated $160M annual revenue came from healthcare companies?
And how much should the healthcare industry invest in cybersecurity? $20B? $50B? $100B?
Who benefits from cybersecurity investment?
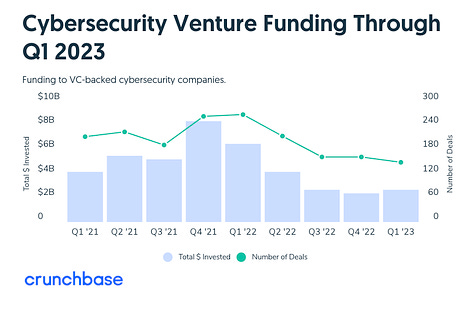
VC firms raised record amounts of money from their limited partners over the past two and a half years. These firms’ partners frequently speak about “dry powder,” waiting to deploy this yet-to-be-invested cash into the right company that can deliver the best returns.
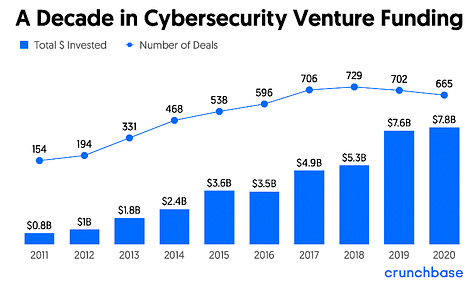
These venture capitalists poured $86B into cybersecurity companies over the last ten years. Investment increased twenty-eightfold between 2011 and 2021. These investments created dozens of so-called unicorns–companies valued at over a billion dollars–many appearing in just the last three years.
Making a very unscientific guess that the average investment returned 10%, the cybersecurity market has generated almost a trillion dollars, most of which has gone back into the coffers of VCs, their LPs, and a handful of company founders and early employees.
Meanwhile, the global economic impact of cybercrime is roughly one trillion dollars annually.
What conclusions can we make?
We aren’t investing enough; when we do, we invest for the wrong reasons.
I couldn’t find a quote from a VC partner saying, “We are waiting to invest this money until we find a company that can decrease the frequency and cost of breaches to customers and reduce the total economic impact of cybercrime.” It doesn’t appear to be a significant consideration to their investment theses.
I’ve heard VCs say, “We are looking to invest in companies that can demonstrate a path to $100M in annual recurring revenue.” They get paid to make returns, so expecting them to act otherwise is, well, foolish.
The problem is, as we’ve discussed above, a company making it to $100M in ARR doesn’t necessarily translate into better customer outcomes. Sure, the vendor makes a lot of money and generates those investor returns. However, the customers laying out tens and hundreds of millions of dollars still feel chronic and acute pain and absorb the costs of vulnerabilities.
To keep pace with the ingenuity and persistence of attackers, we should invest much more in fewer cybersecurity companies. Why fewer? Look at the fine segmentation and fragmentation of the security market. There are dozens of market categories supporting hundreds of vendors. No security practitioner can make sense of the mishmash of features and capabilities or consume the data presented through each of a hundred vendor-supplied dashboards. How do you make that data actionable? Who is going to fix the issues you’ve detected?
Splitting vendors across platforms that are a mile wide and an inch deep and so-called best-of-breed vendors focused on a narrow slice of the problem clearly isn’t helping. Perhaps we need fewer companies with higher quality, more complete capabilities?
Here’s a crazy idea that might align everyone’s incentives. Create companies that declare themselves cybersecurity practitioners. Create a pool where they place revenues, and if the number and cost of breaches go down, those companies earn a 10% premium on their contributed revenues.
Who do you suppose could pay for that?
~~~~~~~~~~~~~~~~~~~~~~
References
This article contains a lot of data, so compiling the resources I used in my research felt worthwhile.
Breach costs
https://www.ibm.com/reports/data-breach
https://blog.checkpoint.com/2023/01/05/38-increase-in-2022-global-cyberattacks/
https://www.csis.org/analysis/economic-impact-cybercrime
https://cybersecurityventures.com/hackerpocalypse-cybercrime-report-2016/
https://www.tandfonline.com/doi/full/10.1080/10920277.2022.2034507
Investments
https://about.crunchbase.com/cybersecurity-research-report-2021/
https://news.crunchbase.com/cybersecurity/funding-drops-ai-quantum-q1-2023/
https://www.securityweek.com/whats-going-cybersecurity-vc-investments/
https://www.securityweek.com/whats-behind-surge-cybersecurity-unicorns/
https://beinsure.com/ranking/biggest-cyber-unicorn-startups-in-world/
Spending
https://www.idc.com/getdoc.jsp?containerId=prUS50498423
https://www.alliedmarketresearch.com/healthcare-cyber-security-market
Blame
https://securityboulevard.com/2021/05/ransomware-attack-disrupts-scripps-health/
https://techcrunch.com/2017/06/01/onelogin-admits-recent-breach-is-pretty-dang-serious/
https://techcrunch.com/2022/12/22/okta-breach-source-code-github/
https://jumpcloud.com/support/mandatory-jumpcloud-api-key-rotation