An Imagined Town Hall With BlackCat Regarding Their Change Healthcare Extortion Process
Addressing the nightmare of dealing with United
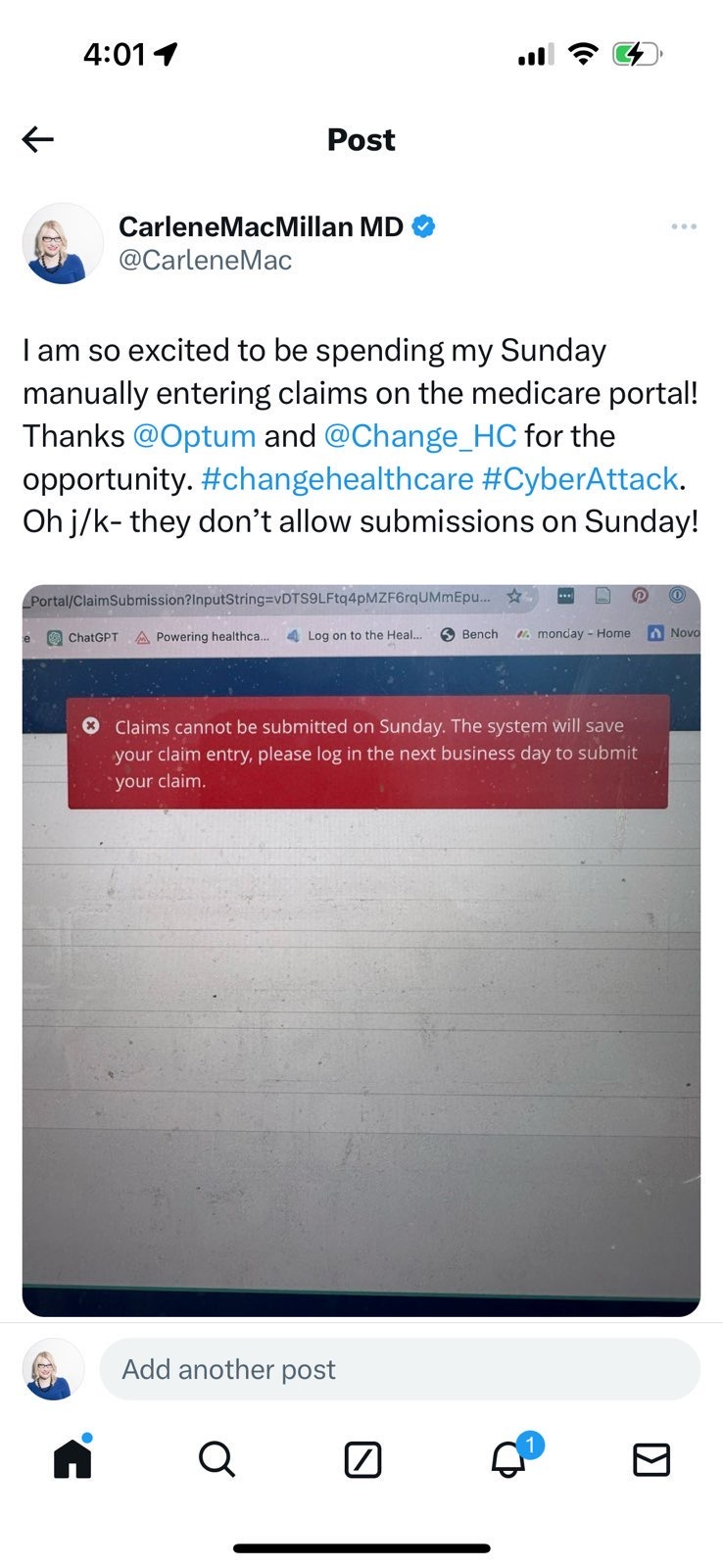
Today's The Frontier Psychiatrist post is an imagined meeting where the BlackCat cyber hackers discuss why they haven't gotten paid from United Healthcare, yet. I was going to write a post about how to solve the change healthcare problem for individual practices, but apparently, that system is down on Sundays, just like the Medicare claims submission process:
Prior Coverage of the United Healthcare and Change Healthcare Cyber Attack include:
(Note: Our article identification product is down, for the time being).
[A Dark Warehouse, somewhere in Eastern Europe, this transcript was—with some irony—leaked from BlackCat HQ]
Thank you so much for coming, we appreciate your attention.
I am going to request that all cameras be off for this, out of respect for the culture at Optum.
I look forward to answering your questions. For the transcript, I just wanna make it clear that our transcribing system uses Change Healthcare, on the backend, which frankly again, is surprising to us, but the questions aren't gonna be transcribed in the written transcript of this all-hands meeting, so if you're reviewing it, you're just gonna have to guess at what the questions were. Luckily, this is a live all-hands for the BlackCat RaaS team, so it shouldn't be a problem. Just for anybody reading later, it will be confusing.
Q.
Thanks, that's a great question. Frankly, this has been one of the more difficult ransom situations we've had to deal with. Usually, people who have committed a massive theft of private information and lockdown their systems are eager to resolve the situation and pay the ransom. Well, they may not be anxious to pay the ransom, but it's very much in their interest to pay the ransom. United Healthcare, on the other hand, is forcing us to go through their phone tree, and so we're just having to say representative, over, and over again, and every third call ends up with us dropped. We have shut down all of American healthcare operations, but apparently, we need to submit a prior authorization for a ransom attempt.
Q.
On the upside, united has been clear about that. They prefer all their ransom attempts to be by fax. So we had to get a fax machine. One of us thought we would be able to use a fax emulation. But their technology is so old, I get bounced on that also, so we had to find a secondhand fax machine.
Q.
Thank you, great question. It turns out the fax number that we used initially is nonworking. Ironically it's the number they provided us with, on the top of the form they said all the ransom requests had to come from, which was confusing because we didn't think there were other ransom requests. It turns out their whole business is structured around “ransom requests,” except it's not for the data, it's for human health. Thanks for the question, Next?
Q.
We've been told we've been told to extort a ransom we needed to ask for an expedited appeal, and we didn't do that initially. So now we have to wait for a regular peer review. This was also surprising, honestly, because we were surprised they had extortionist on staff, but we have to do a peer-to-peer with one of our extortionist hackers and one of their extortionist hackers, who hast to determine if our ransom request is… How do they put it? Oh, reasonable and customary.
Q.
Yes. They're so familiar with the concept of holding peoples’ information hostage that they just have a whole process for this.
Q.
Do we need to use a modifier code when we are submitting more than one data theft ransom request at the same time?
It wasn't clear if we should be using modifier 59.
Frankly, we didn't even know what that was. We didn't have that field in our initial ransom request. The system, I gotta tell you, we were in there for hundreds of days before we locked down, but we were not prepared for its level of dysfunction.
Q.
We were told it has to go through a first-level peer-to-peer. The good news is that has been scheduled.
Q.
The bad news is that it's scheduled for 14 days from now.
Oh, sorry, I'm just getting a message, it's been denied. But we do have the option for…a second-level appeal.
Q.
Apparently… that also needs to be filed by fax.
Q.
This is why we're getting more systems able to fax. Thanks for asking.
Q.
Normally, we set the price on a ransom, but again apparently they have a ransom rate card. It is a percentage of their normal ransom rate? This is also something we are appealing to.
Cats, this is a very frustrating process, and not at all what we are used to. When we hijack a company, nation-state, or person, we like to get paid and get it back to our victims as soon as possible— that just moves things along! This is just not how they work over at United. We were told—in no uncertain terms—they have a system.
Q.
Sorry, had a system.
Q.
Ironically, they said the ransom requests have to be routed through Change, because that has the “ransom system” that they're using, and it's causing a bit of a backup in the process of submitting a ransom request. We can only do it through the process that we have encrypted.
Q.
Of course, we exfiltrated the data first! But when we looked at the source code for the product that they used to accept the ransom request, it turns out it's been corrupted for the last three years, and didn't work for anybody. So it won't work for us either. Nobody noticed, because, as we had mentioned previously, all of their IT has been outsourced to India and other countries, so they don't have anyone who's familiar with it in-house. Also, it was written in COBOL.
Q.
Look, we are optimistic, we are on a second-level appeal, and we're confident we're going to get the ransom we requested. It's over 6 TB of data. I know it's causing some cash flow difficulties for our organization, but on the upside, we connected with a great bank over at Optum, who has offered to lend us the money to finance our operation while we go through the difficult process of re-submitting our ransom request.
Thank you, it's been great talking with you all, and we're hopeful that we're going to make a lot of money on this extortion. I have to say, we may want to look at non-US healthcare for our next extortion attempt because these systems are just more archaic than we had planned.
Thanks, and let's make sure to remember, that no one stands in our way! By the way, this conversation needs to be confidential. We can't have the image of us as brilliant criminal masterminds being dashed by the difficulties we've encountered. We've got a big fish on the line.
Q.
Yes, our usual security protocol is to drug everyone senseless so they don't remember what was discussed. However, there has been a glitch. Usually, we would wipe all of your memories with midazolam or another amnestic, but unfortunately, it turns out that our pharmacy supplier for that also uses change healthcare—the dispensing machine we kept in the headquarters was a product made by McKesson Information Technologies, which it turns out is also part of…Change Healthcare.
[phone rings]
Oh, this is Optum on the line, I got to take this.
'[20 min later]
So, I’m going to be setting up the process of creating an OptumPay account for each of us. I am assured, however, that this will be “Our Live’s Best Scam (TM)” by the folks at Optum.



P.S. this is the funniest damn thing I’ve read on the internet today, it’s too bad it’s real.
I am fluent in COBOL if anyone needs me. But it’s going to cost them.