Today I’m going to show you how you can protect your online accounts (like Google, Binance, Facebook, Twitter, etc.) with your hardware wallet (like Trezor or Ledger).
This results in ultimate security: for a hacker to get to your account, they would have to either: obtain your seed phrase (which you backed up on paper so it can’t be done remotely) or steal your hardware wallet and know the pin (physical thread).
After you set up everything correctly, you can even publish your login and password to your Google account and still be safe. Mindblowing, I know.
Before we get to the how-to, let’s discuss why using Trezor is better than a popular YubiKey.
Why Trezor is better than a YubiKey
YubiKey is excellent and offers the same security as described above: once configured, you can even publish login credentials to the web meaning nobody can access your account unless they have the physical device.
Here is where YubiKey falls short: backup.
If you only configure one YubiKey and it breaks, or you lose it, now you’re the one who can’t get into your online account! Problem.
So what do people do? Buy multiple YubiKeys, configure multiple YubiKeys to their online accounts, carry one YubiKey with them at all times, and store other YubiKeys in secure locations.
This way, if they lose one YubiKey, they always have the backup one.
But it’s problematic:
Not all services allow you to configure multiple hardware keys.
When you create a new online account (which for most of us is often), you need to have that backup hardware key handy to configure it as a backup. That will likely mean the backup YubiKey is in the same location as the primary one, so if there is a fire, you lose everything.
Imagine you lost your primary YubiKey and, thankfully, have been able to use the backup one to sign in to all your accounts. Now what? You must buy a new backup YubiKey, go to each online account, configure a new backup hardware key, etc. So inconvenient!
But thankfully, there is a better way: Trezor.
With Trezor, the seed phrase is your backup.
If your Trezor breaks or is lost, you can configure a new one with the same seed phrase and retain access to all your online accounts.
How to configure
I’ll walk you through an example of something popular most of us probably own: a Google account.
Go to: https://myaccount.google.com/ and sign in to your Google Account.
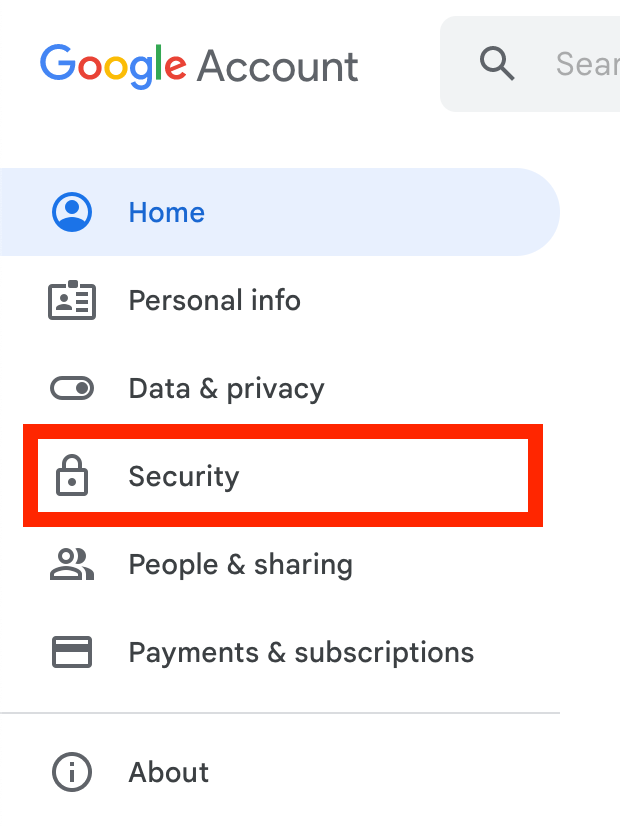
On the top left, click ‘Security’.
’
In the ‘Signing in to Google’ card, click ‘2-Step Verification’
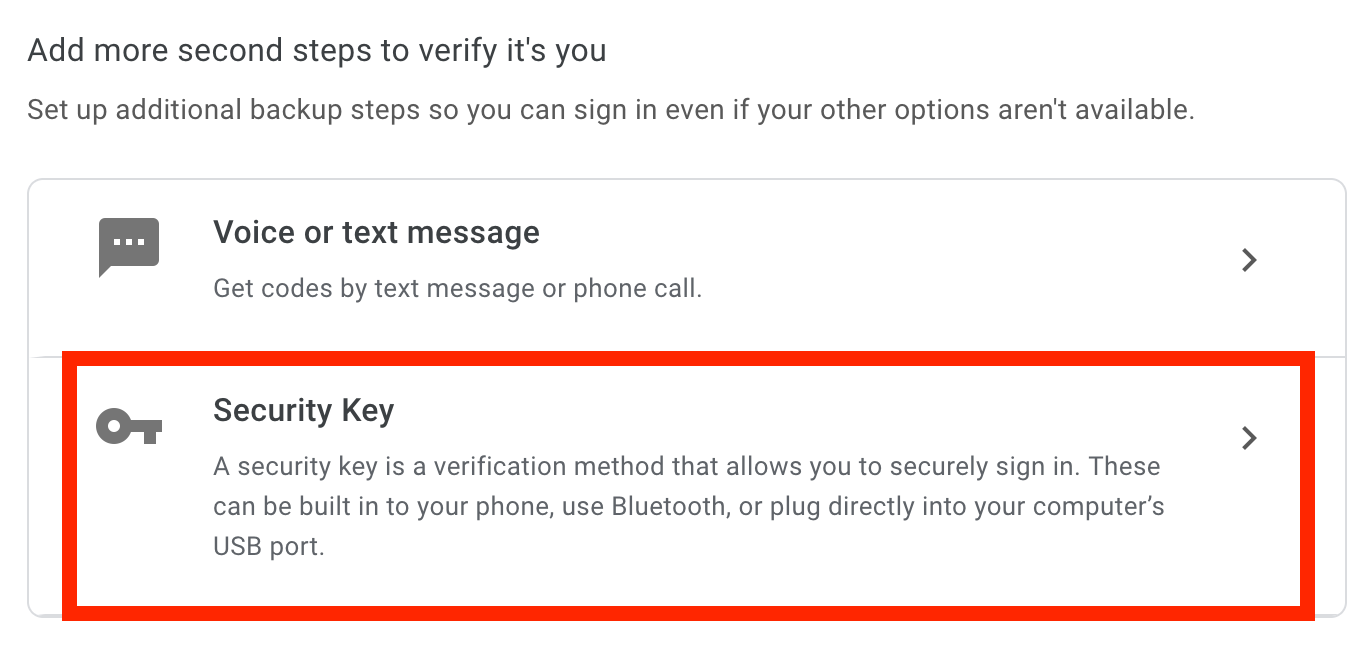
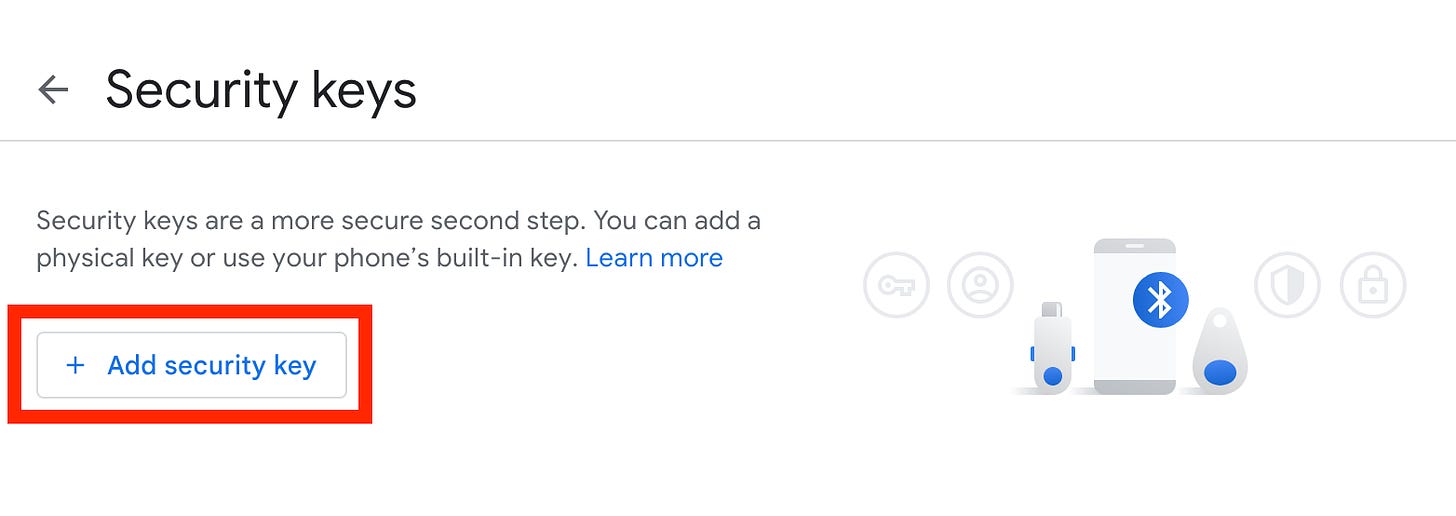
Under ‘Add more second steps to verify it’s you’, click ‘Security Key’ and then ‘Add security key’
It’s time to connect your hardware wallet - I’m using Trezor. I keep my Trezor Suite off to prevent passphrase prompts (it would still work, prompting for a passphrase is just an additional annoyance here). Connect my Trezor and enter the PIN.
Select ‘Physical’ and click ‘Next’
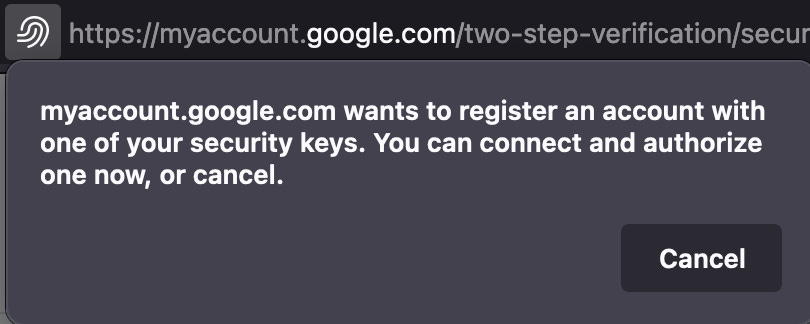
This is what your Firefox browser shows (if you use a different browser, you’ll see a similar prompt):
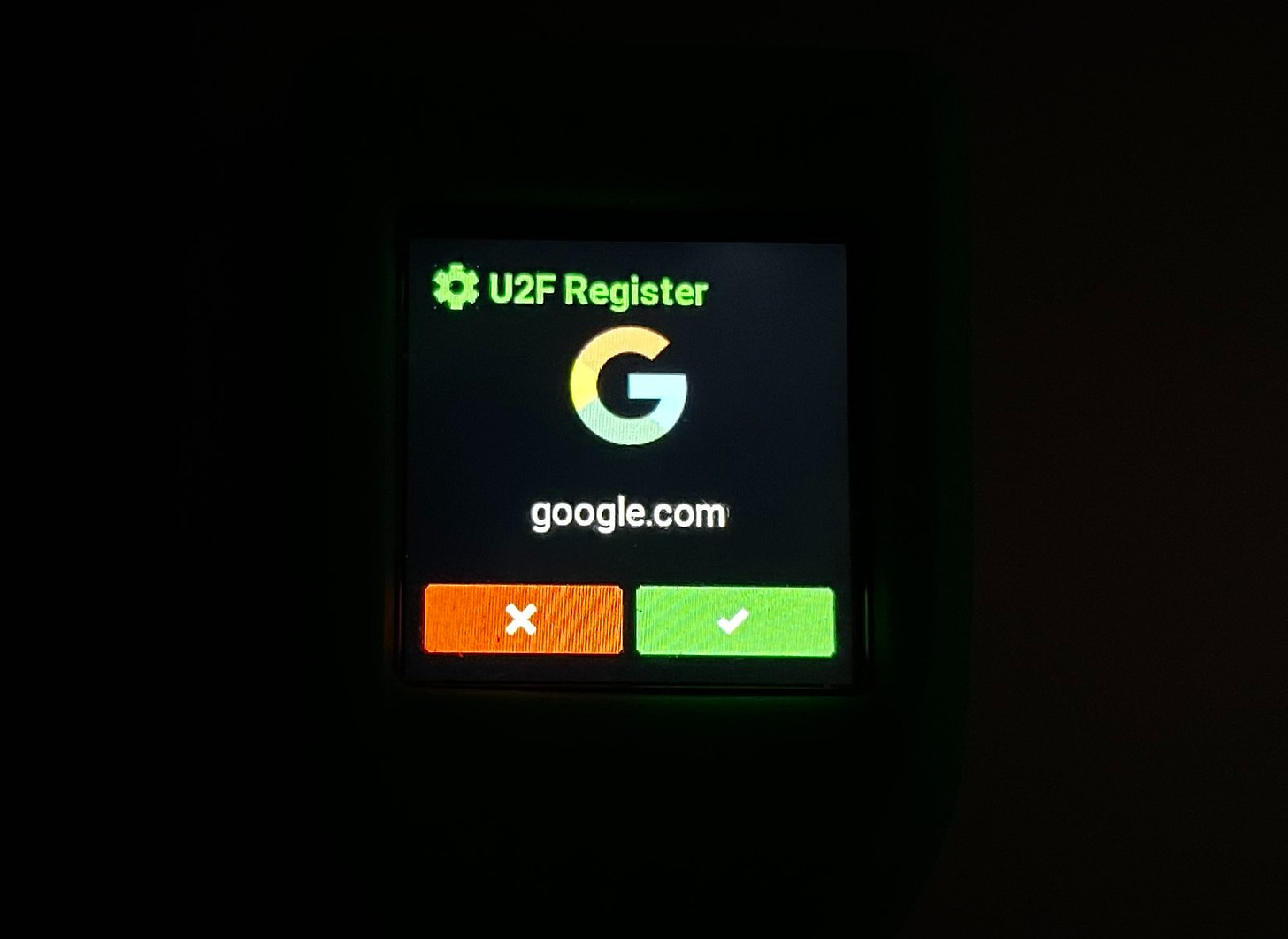
And this is what your Trezor displays:
Confirm on your Trezor device.
Give your hardware key a name, and click ‘Next’.
Congratulations, you’ve just configured the most secure method of authentication possible.
Any other less secure form of authentication is now an additional method of attack for hackers. For example, if your additional authentication method is an SMS code. An attacker can now use a SIM swap attack to go around your physical security key.
This is why disabling all other second factor authentication methods is so critical.
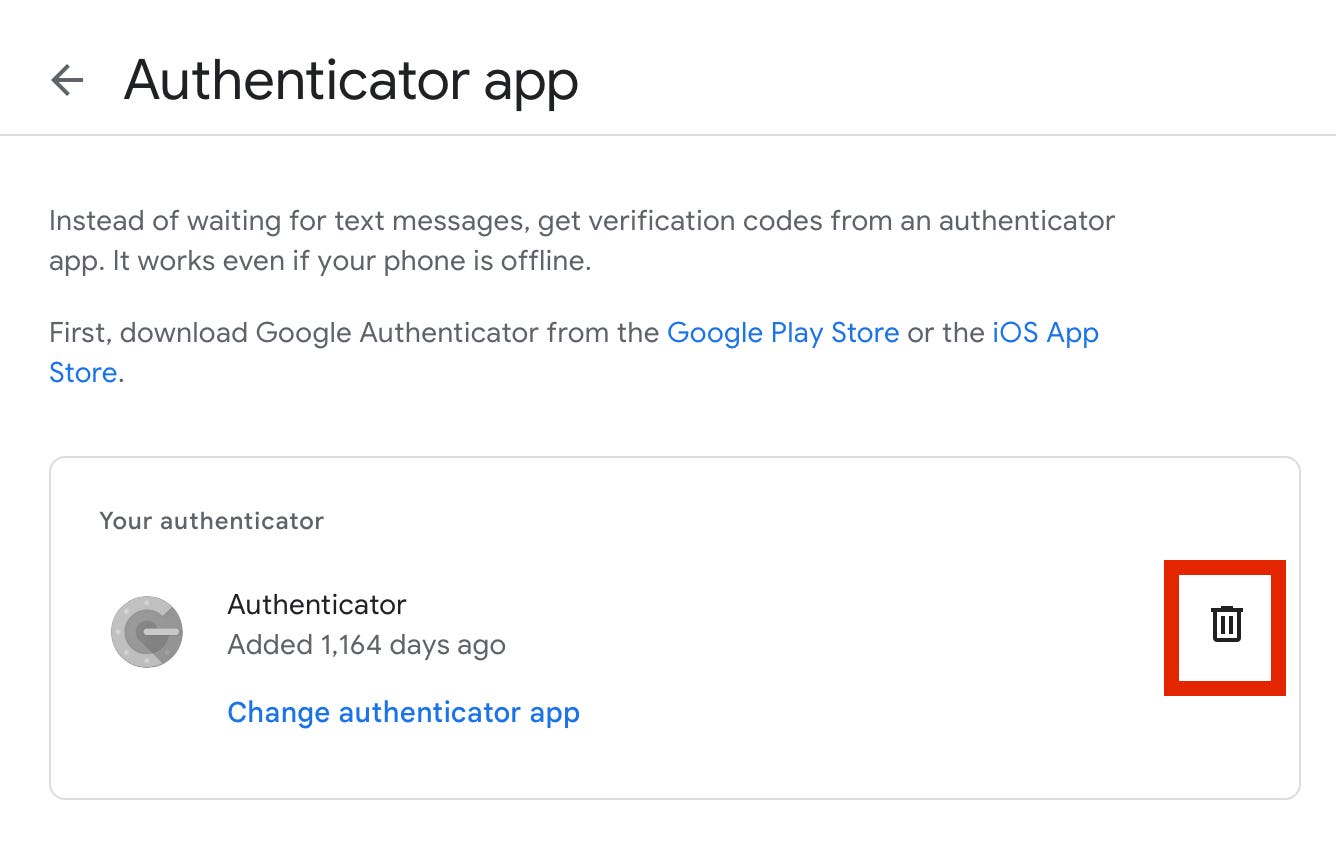
For example, I remove my authenticator app:
I also purposefully remove all ways to identify myself through a different email address and/or a phone number.
The point is to configure your account so there is no way around your physical hardware key (your Trezor device).
Where else can I use it?
There are many online services supporting hardware keys. You’ll find an ever-growing list here:
Can I use Ledger?
Yes, you can use Ledger. However, they’re not clear whether or not if your Ledger breaks or you lose it, and you restore your seed phrase on a different Ledger device, your hardware key authentication will still work.
Here they say:
If you delete and restore your recovery phrase on the same Ledger hardware wallet, you simply need to reinstall the Fido U2F app to regain access to your FIDO-protected account.
It’s not clear if ‘the same Ledger hardware wallet’ means the same model or the same piece.
Here Ledger says:
Our entropy-leading random number generator (RNG) for hardware wallet 24-word mnemonic phrases is also a storage redundancy for the user’s U2F identity, an improvement over Google Authenticator. Should users lose their hardware device, have it stolen, or it malfunctions, their U2F authentication is saved — tied to their unique identity.
So they’re not clear on this. I might do my own experiment in the future using two separate Ledger devices. Until then, I recommend Trezor.
Does my passphrase influence the authentication?
On Trezor, your passphrase does not influence the authentication - no matter what passphrase you enter, you’ll always be able to sign in to an online service. What matters here is the seed phrase.
How is that more secure than Google Authenticator?
TOTPs (Time-based One-Time Passwords) are better than just a login and password but can be easily stolen with a phishing attack. Use a physical security key for ultimate protection.










Ok cool. Refering to my previous comment to a more recent article from you: Is this what you mentioned the only reason for you to recommend Trezor over Ledger?